7 Key Insights into the Rise of Intelligent Intrusion Detection: From SnortML to Autonomous Agents
For decades, intrusion detection systems (IDS) relied on a simple, binary question: Does this packet match a known signature? This approach worked well for well-documented threats, but as cyberattacks grew more sophisticated, it became clear that static pattern-matching was no longer sufficient. The advent of machine learning (ML) and agentic artificial intelligence (AI) has fundamentally shifted the paradigm—moving from "Does this match?" to "Does this make sense in context?". In this article, we explore seven critical developments that define this transformation, from the integration of ML into Snort (SnortML) to the rise of autonomous decision-making agents. These innovations are not just incremental upgrades; they represent a new architecture for intrusion detection—one that mirrors organic intelligence itself.
1. The Limits of Signature-Based Detection
Traditional IDS like Snort rely on databases of known attack signatures—binary strings or patterns that exactly describe malicious traffic. While effective against established threats, signature-based systems are blind to zero-day exploits, polymorphic malware, or subtle variations of known attacks. They require constant manual updates and produce a high volume of false positives, overwhelming security analysts. The core limitation is the inability to reason about context: a packet that matches a known malicious pattern might be benign in a normal application, and an anomalous pattern might be completely novel. This gap creates the need for detection that understands rather than just matches, paving the way for machine learning solutions like SnortML.
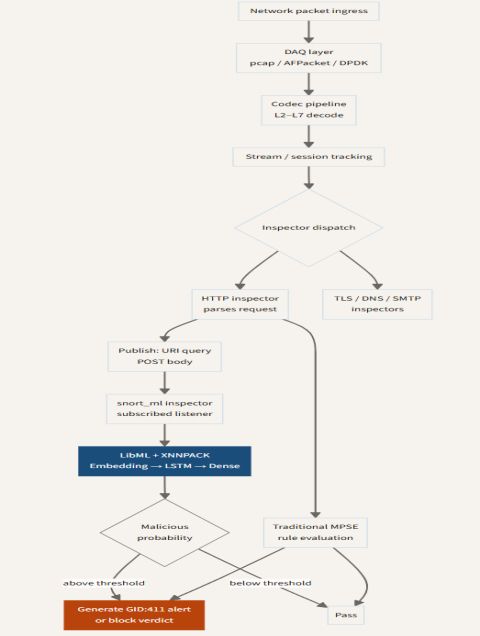
2. SnortML: Embedding Machine Learning Directly into the Sensor
SnortML represents a breakthrough by embedding lightweight machine learning models directly into the Snort sensor, running alongside traditional signature rules. Instead of separate analysis infrastructure, SnortML processes network traffic in real time, applying models trained to detect anomalies and behavioral outliers. The key advantage is that the sensor can now flag traffic that deviates from baseline—e.g., an internal host suddenly communicating with an external IP using an unusual protocol—without needing a specific signature. This reduces latency and enables detection of previously unseen attack patterns. SnortML can be deployed with minimal overhead, making it accessible for organizations that lack dedicated ML teams.
3. The Shift from Pattern Matching to Contextual Reasoning
The fundamental change introduced by ML and agentic AI is the shift from raw pattern matching to contextual reasoning. Traditional IDS ask: Is this byte sequence in my database? Modern systems ask: Does this sequence of events comport with what we know about normal behavior? This context-aware approach considers factors like time of day, user role, device type, and recent network activity. For example, a login attempt from an unusual geographic location might be benign if it originates from a known VPN, but suspicious if it comes from a non-corporate network. By evaluating context, false positives plummet, and detection extends to attacks that don't have a known signature. This evolution is powered by AI models that learn the “normal” patterns specific to each environment.
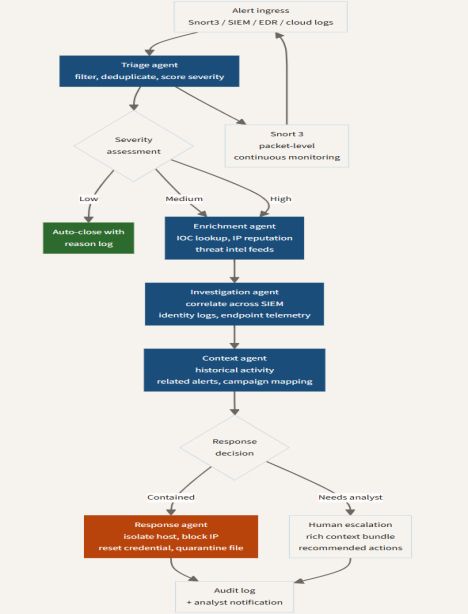
4. Agentic AI: Autonomous Decision-Making in Security Operations
Agentic AI takes contextual reasoning a step further by introducing autonomous agents that can make decisions and take actions without human intervention. In the context of intrusion detection, an agentic AI system might analyze alerts from multiple sensors, correlate them with threat intelligence, and automatically block a suspicious connection, contain a compromised host, or escalate an incident to a human. These agents are not just reactive; they can proactively hunt for threats by adjusting detection thresholds or deploying decoys. The architecture is modular: agents specialize in different tasks (analysis, response, reporting) and communicate via standards like STIX/TAXII. This mirrors the organic intelligence of a distributed immune system, where local sensors (like SnortML) feed into higher-order reasoning centers.
5. Machine Learning Models Trained on Enterprise-Specific Telemetry
One of the most powerful aspects of the new detection architecture is the ability to train models on telemetry from the specific enterprise environment. Rather than using generic threat intelligence feeds, organizations can ingest logs from their own endpoints, network flows, cloud services, and identity providers. This data, rich with behavioral signals, enables models to learn the unique “personality” of the network. For example, a model can recognize that a particular server rarely makes outbound connections, so any outbound traffic from it is automatically suspicious. This approach dramatically reduces false positives and improves detection of insider threats and lateral movement. However, it requires careful data management and privacy considerations.
6. Challenges: Adversarial Machine Learning and Model Fatigue
While AI-enhanced intrusion detection offers immense benefits, it also introduces new challenges. Adversarial machine learning is a growing concern: attackers can craft inputs that deliberately fool ML models, such as injecting subtle noise into network packets to evade anomaly detection. Additionally, organizations face model fatigue—the maintenance burden of retraining models to keep them accurate as networks evolve. False positives can still occur, and without proper tuning, analysts may lose trust in AI-generated alerts. The solution lies in hybrid approaches that combine ML with rule-based validation and human-in-the-loop feedback loops. Agentic AI systems must incorporate adversarial robustness and allow security teams to oversee and modify model behavior.
7. The Future: Autonomous Cooperative Networks of Sensors and Agents
Looking ahead, the architecture of intrusion detection will evolve into a cooperative network of intelligent sensors and autonomous agents. Imagine hundreds of SnortML instances across an enterprise, each continuously learning and sharing insights with a central AI “orchestrator”. When a sensor detects an anomaly, it doesn’t just fire an alert—it communicates with neighboring sensors to confirm the pattern, then triggers a coordinated response. This mimics the way biological immune systems mount a systemic defense against localized threats. As edge computing and 5G expand, detection will move closer to the source, with lightweight models running on IoT devices. The ultimate goal is a self-healing network that adapts in real time, where the question shifts again—from "Does this make sense?" to "How do we ensure resilience?".
The evolution from signature-based detection to machine learning and agentic AI is not merely a technological upgrade—it is a conceptual revolution. Today's intrusion detection systems are no longer passive observers that match patterns; they are active participants that think, reason, and act. SnortML exemplifies how existing tools can be augmented with onboard intelligence, while agentic AI promises a future of autonomous, cooperative defense. Yet challenges remain, from adversarial attacks to the need for continuous model tuning. Ultimately, the organizations that thrive will be those that embrace this new architecture—one that sees the network as a living entity whose intelligence emerges from the interaction of many small, smart sensors.
Related Articles
- 7 Essential AI and Machine Learning Use Cases in Finance You Need to Know
- Mastering the Anthbot M9: A Complete Guide to iPhone-Controlled Lawn Care
- Silent Data Sinks: How Poor Quality Is Crippling Generative and Agentic AI in Production
- Beat the Heat with Sony's Reon Pocket Pro Plus: A Complete User Guide
- Uber's Bold New Plan: Turning Drivers into a Real-Time Sensor Network for Autonomous Vehicles
- Global Law Enforcement Stuns Cybercrime: Four IoT Botnets Dismantled After Targeting 3 Million Devices
- Guarding Your AI Pipeline: A Practical Guide to Data Quality for ML, Generative AI, and Autonomous Agents
- Creating a Conversational C-3PO Head: An AI Project